Let's learn about Data Protection via these 121 free stories. They are ordered by most time reading created on HackerNoon. Visit the /Learn Repo to find the most read stories about any technology.
1. AI and Personal Data: Does GPT-3 Know Anything About Me?
 What do AI's know about you and can you opt out? Large Language Models are going to be used in search engine outputs and it's time to prepare!
What do AI's know about you and can you opt out? Large Language Models are going to be used in search engine outputs and it's time to prepare!
2. 6 Data Cybersecurity Challenges with Cloud Computing
 It is important to keep your data safe and secure. Here are six challenges in that hosting your data on the cloud can pose and how your data security can help.
It is important to keep your data safe and secure. Here are six challenges in that hosting your data on the cloud can pose and how your data security can help.
3. Federal Biometrics: How Does the Government Use Biometrics Data?

4. Common RAID Failure Scenarios And How to Deal with Them
 Most businesses these days use RAID systems to gain improved performance and security. Redundant Array of Independent Disks (RAID) systems are a configuration of multiple disk drives that can improve storage and computing capabilities. This system comprises multiple hard disks that are connected to a single logical unit to provide more functions. As one single operating system, RAID architecture (RAID level 0, 1, 5, 6, etc.) distributes data over all disks.
Most businesses these days use RAID systems to gain improved performance and security. Redundant Array of Independent Disks (RAID) systems are a configuration of multiple disk drives that can improve storage and computing capabilities. This system comprises multiple hard disks that are connected to a single logical unit to provide more functions. As one single operating system, RAID architecture (RAID level 0, 1, 5, 6, etc.) distributes data over all disks.
5. EU Drafts Data Regulations for Voice Assistant Developers
 On March 2, 2021, the European Data Protection Board (EDPB) released Guidelines on Virtual Voice Assistants (VVAs) to protect users’ privacy.
On March 2, 2021, the European Data Protection Board (EDPB) released Guidelines on Virtual Voice Assistants (VVAs) to protect users’ privacy.
6. 7 Data Analysis Steps You Should Know
 To analyze data adequately requires practical knowledge of the different forms of data analysis.
To analyze data adequately requires practical knowledge of the different forms of data analysis.
7. Why Are Businesses Raising Equity with Crowdfunding?
 Equity crowdfunding was not the easiest choice to make, but it kept us true to our core values of trust, transparency, and user-centricity.
Equity crowdfunding was not the easiest choice to make, but it kept us true to our core values of trust, transparency, and user-centricity.
8. Top Emerging Cybersecurity Threats and How to Prevent Them From Happening to You
 The fact is cybercrime is exponentially increasing. For all security threats, technical literacy and awareness are essential to protect yourself from such crime
The fact is cybercrime is exponentially increasing. For all security threats, technical literacy and awareness are essential to protect yourself from such crime
9. How the Blockchain Will Improve Data Security

10. Synthetic Data’s Role in the Future of AI
 Thanks to advanced data generation techniques, synthetic data can replicate real-world scenarios with high levels of accuracy.
Thanks to advanced data generation techniques, synthetic data can replicate real-world scenarios with high levels of accuracy.
11. The Best Cybersecurity Practices for Data Centres
 Read on to learn about the specifications of data center security and the risks that threaten it. Discover the cybersecurity best practices that you need.
Read on to learn about the specifications of data center security and the risks that threaten it. Discover the cybersecurity best practices that you need.
12. How to Activate Disappearing Messages on Instagram
 In this post, you will get complete knowledge of how to hide Instagram messages without deleting them.
In this post, you will get complete knowledge of how to hide Instagram messages without deleting them.
13. Current Web3 Development is Similar to the Internet Boom of the Late 90s
 SIMBA Chain started working on its first blockchain projects for organizations like the US Navy, Boeing, and other defence contractors.
SIMBA Chain started working on its first blockchain projects for organizations like the US Navy, Boeing, and other defence contractors.
14. Assessing Your Organization's Customer Data Maturity
 Investing in customer data is a top priority for marketing leaders.
Investing in customer data is a top priority for marketing leaders.
15. Proposition 24: What you Need to Know About Data Privacy America
 Californians have spoken: Proposition 24 will soon expand data privacy protections in the largest state in America.
Californians have spoken: Proposition 24 will soon expand data privacy protections in the largest state in America.
16. Decentralized Storage and Data Privacy for Developers
 Arcana Network runs on its blockchain, independent of a large centralized entity. have no central storage. Data Privacy on the blockchain.
Arcana Network runs on its blockchain, independent of a large centralized entity. have no central storage. Data Privacy on the blockchain.
17. The Importance of Web Penetration Testing
 A pen test or penetration test is a modeled cyber-attack on your computer system to look for vulnerabilities that could be exploited.
A pen test or penetration test is a modeled cyber-attack on your computer system to look for vulnerabilities that could be exploited.
18. Exactly How Secure is Web 3
 Ever wonder what data privacy will look like in Web 3? Yes, everyone is. But don't fret. This article explains web 3 security issues.
Ever wonder what data privacy will look like in Web 3? Yes, everyone is. But don't fret. This article explains web 3 security issues.
19. We Open Sourced Datanymizer: in-Flight Template-Driven Data Anonymization Tool
 Datanymizer is an open-source, GDPR-compliant, privacy-preserving data anonymization tool flexible about how the anonymization takes place
Datanymizer is an open-source, GDPR-compliant, privacy-preserving data anonymization tool flexible about how the anonymization takes place
20. Three New Dimensions to Ransomware Attacks Emerge During Pandemic
![]() Three significant new trends in cyber-attacks have emerged from the Covid-19 emergency. Firstly, a new generation of attack software which has been developing since last summer has come of age and been deployed. Secondly, the business model for extracting payment from victims has changed so that there are multiple demands for payments of different kinds, including auctioning off data. Thirdly, the kinds of clients that the gangs are targeting seems to have shifted.
Three significant new trends in cyber-attacks have emerged from the Covid-19 emergency. Firstly, a new generation of attack software which has been developing since last summer has come of age and been deployed. Secondly, the business model for extracting payment from victims has changed so that there are multiple demands for payments of different kinds, including auctioning off data. Thirdly, the kinds of clients that the gangs are targeting seems to have shifted.
21. How Can Password-Free Identity Verification Safeguard User Privacy?
 Traditional identity verification methods usually have security risks. Unlike these methods, FIDO-based identity verification is much safer and convenient.
Traditional identity verification methods usually have security risks. Unlike these methods, FIDO-based identity verification is much safer and convenient.
22. Is The Future Of Encryption On The Line?
 In a world where encryption of our messaging apps is at stake, is there a solution that works? Aside from the traditional WhatsApp and Signal, there's Usecrypt.
In a world where encryption of our messaging apps is at stake, is there a solution that works? Aside from the traditional WhatsApp and Signal, there's Usecrypt.
23. Data Backup Strategy To Reduce Data Loss
 Backing up the data is one of the most important processes for businesses. It requires creating a copy of all your data and storing it.
Backing up the data is one of the most important processes for businesses. It requires creating a copy of all your data and storing it.
24. Reasons Why Data Privacy Matters
 Data privacy is one of the hottest topics in tech conversation. But what's the deal with it? Is it good? Is It bad? Keep reading to find out.
Data privacy is one of the hottest topics in tech conversation. But what's the deal with it? Is it good? Is It bad? Keep reading to find out.
25. Redefining Privacy and Data Ownership: An Interview with ARPA Founder, Felix Xu
 A conversation with Felix Xu, CEO of ARPA, on data utility and ownership, the NFT ecosystem, and much more.
A conversation with Felix Xu, CEO of ARPA, on data utility and ownership, the NFT ecosystem, and much more.
26. Confidential Computing: How Intel SGX is Helping to Achieve It
 Learn more about confidential computing and how Intel SGX is used to encrypt sensitive data in memory, enabling compliant collaboration between organizations.
Learn more about confidential computing and how Intel SGX is used to encrypt sensitive data in memory, enabling compliant collaboration between organizations.
27. Bringing Back Data Ownership to Humans With Decentralizion
 Are we ready as humans to take the data ownership back? Here is a use case for you.
Are we ready as humans to take the data ownership back? Here is a use case for you.
28. What Are The Challenges of Monetizing and Selling Data?
 There have been great advancements in monetization opportunities in the last decade, but there are still challenges when it comes to generating big data analyti
There have been great advancements in monetization opportunities in the last decade, but there are still challenges when it comes to generating big data analyti
29. Organizing Your Business Statistics to Achieve Success
 It is not an easy task to keep your business data organized; however, it is an important thing to do. Organizing data includes a lot more than putting all your papers in place and clearing the clutter on your desk. To have your statistics well organized, you have to create a system and procedures for every department available in your company. The following are top ideas o0n how you can get your small business statistics that can help in increasing the productivity of the business.
It is not an easy task to keep your business data organized; however, it is an important thing to do. Organizing data includes a lot more than putting all your papers in place and clearing the clutter on your desk. To have your statistics well organized, you have to create a system and procedures for every department available in your company. The following are top ideas o0n how you can get your small business statistics that can help in increasing the productivity of the business.
30. The Importance of IoT Security
 Let's look at why security is very important for IoT devices
Let's look at why security is very important for IoT devices
31. True Cost of Cybercrime: What Organizations Should be Prepared For
 Cybercrime is on the rise and, despite the cost of cybersecurity being a stumbling block for many, here is why businesses must implement security measures...
Cybercrime is on the rise and, despite the cost of cybersecurity being a stumbling block for many, here is why businesses must implement security measures...
32. How to Deal with Tech Trust Deficit
 We’re more dependent on tech and e-commerce than ever before, and customers want to know that brands are protecting their data and privacy.
We’re more dependent on tech and e-commerce than ever before, and customers want to know that brands are protecting their data and privacy.
33. Manage Your Emails Like You Manage Your Passwords
 Add an extra security layer for the protection of your emails.
Add an extra security layer for the protection of your emails.
34. How to Prevent Juice Jacking
 Juice jacking occurs when a hacker has infected a USB port with some form of malware or other harmful software.
Juice jacking occurs when a hacker has infected a USB port with some form of malware or other harmful software.
35. Why Did Today Feel like a Black Mirror Episode?
 Are the recent tech giant privacy policy updates of September 2022 pushing us further into dystopia? strfsh live report
Are the recent tech giant privacy policy updates of September 2022 pushing us further into dystopia? strfsh live report
36. Five Promising Startups That May Change the Way We Do Business in 2023 and Beyond
 Judging by the survey conducted by Forbes, we can highlight five trends that will shape business in 2023.
Judging by the survey conducted by Forbes, we can highlight five trends that will shape business in 2023.
37. How To Protect Your Data Against Credit Card Breaches
 Save your credit card information from being hacked by following these tips.
Save your credit card information from being hacked by following these tips.
38. Useful Digital Tools for Nonprofit Attorneys
 We've identified some potential pain points for nonprofit attorneys, where a lack of effective tech can slow down processes or leave holes in security practice.
We've identified some potential pain points for nonprofit attorneys, where a lack of effective tech can slow down processes or leave holes in security practice.
39. 6 Tips to Safeguard Patrons' Privacy at Your Library
 Patron privacy is one of those topics that touches every aspect of a library's operations, and for good reason.
Patron privacy is one of those topics that touches every aspect of a library's operations, and for good reason.
40. How Secure are the Top Frameworks for Development?
 If you've seen headlines like "Top Frameworks", have you wondered why they are considered the best? Are cyber security vulnerabilities considered in this case?
If you've seen headlines like "Top Frameworks", have you wondered why they are considered the best? Are cyber security vulnerabilities considered in this case?
41. California's Current Privacy Rights Under CCPA
 California recently passed a sweeping privacy law that makes it the most privacy forward state in the nation. But, until it gets implemented, there is this thing privacy framework (the CCPA) is the law of the land.
California recently passed a sweeping privacy law that makes it the most privacy forward state in the nation. But, until it gets implemented, there is this thing privacy framework (the CCPA) is the law of the land.
42. How Verifiable Creds, Decentralized Identifiers and Blockchain Work Together for a Safer Internet
 The future of the internet will come with more risks to our data privacy. Fortunately, Blockchain and Decentralized Identifiers can work together to protect.
The future of the internet will come with more risks to our data privacy. Fortunately, Blockchain and Decentralized Identifiers can work together to protect.
43. Combat Online Vaccine Registration Scams With Better Cybersecurity Measures
 Hackers are targeting the online vaccine supply chain and are setting up malicious attacks to have unauthorized access to the organization’s vaccine information
Hackers are targeting the online vaccine supply chain and are setting up malicious attacks to have unauthorized access to the organization’s vaccine information
44. 5 Life-Saving Tips About Cyber Security
 Introduction:
Introduction:
45. 10 Threats to an Open API Ecosystem
 Despite tight economic situations worldwide, the API economy continues to grow.
Despite tight economic situations worldwide, the API economy continues to grow.
46. 10 Secure Online Applications in 2021: No More Spy Spps and Hacker Attacks
 A selection of programs for online privacy. All of them will help you not to fall prey to hackers and keep your data safe.
A selection of programs for online privacy. All of them will help you not to fall prey to hackers and keep your data safe.
47. A Guide To Protecting Sensitive Business Data
 Each year, we’re witnessing growing trends of digitalization and connectivity. However, the more data businesses are storing digitally, the more exposed the data is to breaches.
Each year, we’re witnessing growing trends of digitalization and connectivity. However, the more data businesses are storing digitally, the more exposed the data is to breaches.
48. Data Loss Prevention: What is it, and Do You Need it?
 Data Loss Prevention is a set of tools and practices geared towards protecting your data from loss and leak. Even though the name has only the loss part, in actuality, it's as much about the leak protection as it is about the loss protection. Basically, DLP, as a notion, encompasses all the security practices around protecting your company data.
Data Loss Prevention is a set of tools and practices geared towards protecting your data from loss and leak. Even though the name has only the loss part, in actuality, it's as much about the leak protection as it is about the loss protection. Basically, DLP, as a notion, encompasses all the security practices around protecting your company data.
49. Investing in Cybersecurity to Build a Successful Exchange - With Ben Zhou, CEO at Bybit
 Investing in critical infrastructure is the key to building a successful digital exchange. In this interview, we talk about regulations and cybersecurity.
Investing in critical infrastructure is the key to building a successful digital exchange. In this interview, we talk about regulations and cybersecurity.
50. What's in Store for Privacy and Personal Data Protection in 2022?
 2021 saw many advancements in internet privacy, what does 2022 have in store?
2021 saw many advancements in internet privacy, what does 2022 have in store?
51. 5 Ways to Ensure You Aren’t Sharing Your Workplace Data
 With so much of our lives online, it's too easy for us to make a mistake and accidentally share our workplace data. These easy methods keep your data safe.
With so much of our lives online, it's too easy for us to make a mistake and accidentally share our workplace data. These easy methods keep your data safe.
52. DPA as a Cybersecurity Measure
 When working with a software development outsourcing company or through any third parties make sure you explore the possibilities of DPA.
When working with a software development outsourcing company or through any third parties make sure you explore the possibilities of DPA.
53. Ensuring Privacy with Zero-party Data
 Zero-party data is the future of data collection because it bridges the gap between advertising needs and consumers’ concerns about privacy.
Zero-party data is the future of data collection because it bridges the gap between advertising needs and consumers’ concerns about privacy.
54. 5 Ways to Protect Your Cloud Storage
55. How to Protect Against Attacks Using a Quantum Computer
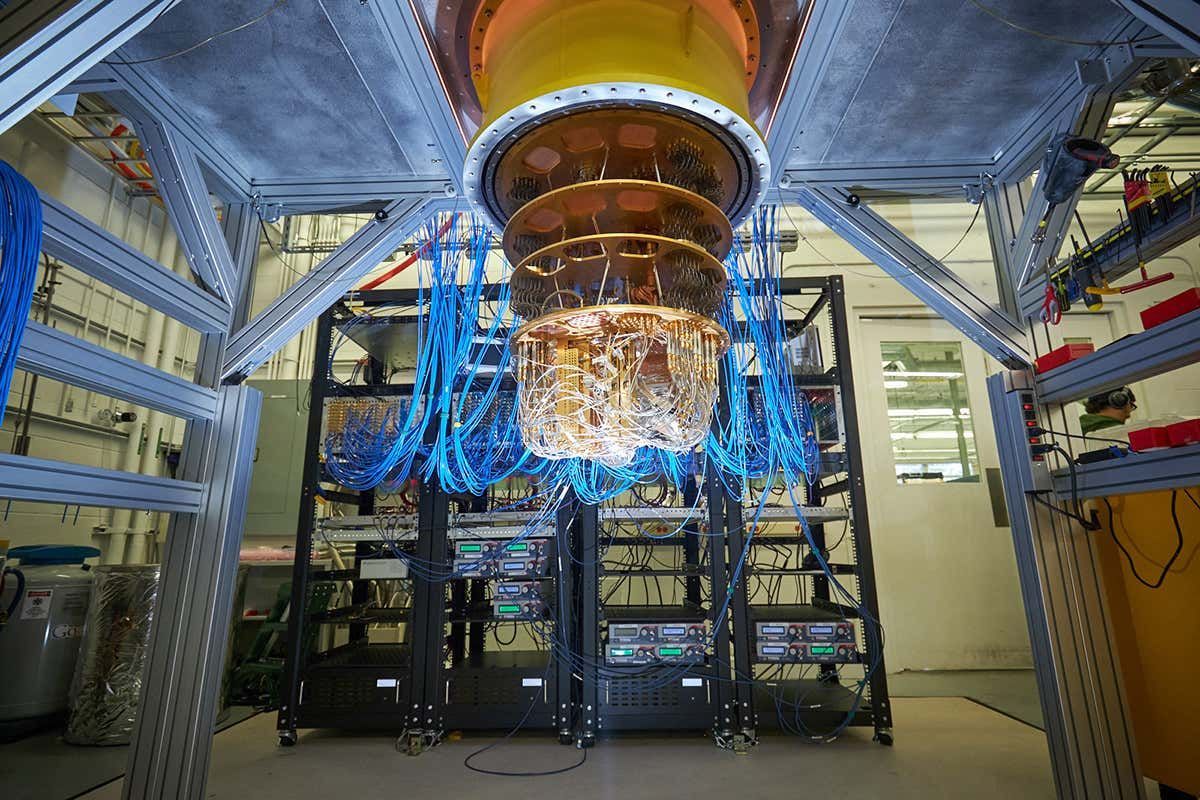 Quantum technologies are steadily entering our life, and soon we will hear about new hacks using a quantum computer. So, how to protect against quantum attacks?
Quantum technologies are steadily entering our life, and soon we will hear about new hacks using a quantum computer. So, how to protect against quantum attacks?
56. Glossary of Security Terms: Same-Origin Policy
 The same-origin policy is a critical security mechanism that restricts how a document or script loaded from one origin can interact with a resource from another origin. It helps isolate potentially malicious documents, reducing possible attack vectors.
The same-origin policy is a critical security mechanism that restricts how a document or script loaded from one origin can interact with a resource from another origin. It helps isolate potentially malicious documents, reducing possible attack vectors.
57. Cybersecurity Is No Longer "Optional"
 Security breaches can cost businesses millions of dollars. It's high time businesses start to realize the importance of cybersecurity strategies.
Security breaches can cost businesses millions of dollars. It's high time businesses start to realize the importance of cybersecurity strategies.
58. How to Secure Office 365 & Windows from Ransomware Attacks
 It’s no secret that we’re living in uncertain times. Many countries are under partial or full lockdown for the past few weeks, making work from home the new norm for the foreseeable future, at least.
It’s no secret that we’re living in uncertain times. Many countries are under partial or full lockdown for the past few weeks, making work from home the new norm for the foreseeable future, at least.
59. 4 Protections that Every Startup Needs
 According to Yahoo Small Business, "approximately 543,000 new businesses are started each month." That seems to be good news until you read the following sentence: "but unfortunately, even more than that shutdown."
According to Yahoo Small Business, "approximately 543,000 new businesses are started each month." That seems to be good news until you read the following sentence: "but unfortunately, even more than that shutdown."
60. Why Businesses Need Data Governance
 Governance is the Gordian Knot to all Your Business Problems.
Governance is the Gordian Knot to all Your Business Problems.
61. How to Protect Yourself Inside the Metaverse: Do NOT Fall Victim to Virtual Maniacs
 Crimes will continue.
Crimes will continue.
62. Benefits of Corporate Data Backup and Best Practices to Keep in Place
 Nowadays, companies are increasingly relying on corporate data backup solutions to guarantee the safety and recoverability of their data. Read on to learn more
Nowadays, companies are increasingly relying on corporate data backup solutions to guarantee the safety and recoverability of their data. Read on to learn more
63. Common Misconceptions About Why VPNs Are Used
 There are some misconceptions about why VPNs are used such as the extent of the privacy that they offer and how well such systems can keep users anonymous.
There are some misconceptions about why VPNs are used such as the extent of the privacy that they offer and how well such systems can keep users anonymous.
64. How an Improved Working Relationship Between Employer and Employee Could be the Key to Cybersecurity
 In a lot of organizations, the focus on cybersecurity has always been on building secure infrastructure and while the idea good in theory, it may not necessarily keep all your data safe. You need to consider the impact of a good working relationship and the understanding of how people think.
In a lot of organizations, the focus on cybersecurity has always been on building secure infrastructure and while the idea good in theory, it may not necessarily keep all your data safe. You need to consider the impact of a good working relationship and the understanding of how people think.
65. 5 Ways to Protect Your Facebook Account from Getting Hacked
 If you're wondering how to stop Facebook hackers, here are 5 easy ways to do so. This guide is beginner-friendly and all discussed methods are free.
If you're wondering how to stop Facebook hackers, here are 5 easy ways to do so. This guide is beginner-friendly and all discussed methods are free.
66. 4 Ways Cities Are Utilizing Data for Public Safety
 Cities have been using data for public safety for years. What new technology is emerging in public safety, and how does it affect you?
Cities have been using data for public safety for years. What new technology is emerging in public safety, and how does it affect you?
67. Securing your SDLC for Open Source Applications
 Creating a secure SDLC isn’t difficult. It might require some adjustment by teams that are not used to it, but it’s a worthy investment.
Creating a secure SDLC isn’t difficult. It might require some adjustment by teams that are not used to it, but it’s a worthy investment.
68. Glossary of Security Terms: HSTS
 HTTP Strict Transport Security lets a web site inform the browser that it should never load the site using HTTP and should automatically convert all attempts to access the site using HTTP to HTTPS requests instead. It consists in one HTTP header, Strict-Transport-Security, sent by the server with the resource.
HTTP Strict Transport Security lets a web site inform the browser that it should never load the site using HTTP and should automatically convert all attempts to access the site using HTTP to HTTPS requests instead. It consists in one HTTP header, Strict-Transport-Security, sent by the server with the resource.
69. Glossary of Security Terms: MitM
 A Man-in-the-middle attack (MitM) intercepts a communication between two systems. For example, a Wi-Fi router can be compromised.
A Man-in-the-middle attack (MitM) intercepts a communication between two systems. For example, a Wi-Fi router can be compromised.
70. Glossary of Security Terms: Session Hijacking
 Session hijacking occurs when an attacker takes over a valid session between two computers. The attacker steals a valid session ID in order to break into the system and snoop data.
Session hijacking occurs when an attacker takes over a valid session between two computers. The attacker steals a valid session ID in order to break into the system and snoop data.
71. Web Application Security: A Broader Perspective
 Security has become an integral part of software development and operations lifecycle. When it comes to web applications, there are well-established patterns and practices to ensure securing the data. Typically most of us consider access control and securing the data at rest and transit for protection. Though these areas are fundamentally important, there are many more things to do to establish overall security of a web application. This article focuses on providing a broader perspective of things, in developing secure software focusing mostly on web applications.
Security has become an integral part of software development and operations lifecycle. When it comes to web applications, there are well-established patterns and practices to ensure securing the data. Typically most of us consider access control and securing the data at rest and transit for protection. Though these areas are fundamentally important, there are many more things to do to establish overall security of a web application. This article focuses on providing a broader perspective of things, in developing secure software focusing mostly on web applications.
72. Why You Should Consider Becoming an Ethical Hacker in 2021
 Ethical hackers are skilled people who are given access to the network, by relevant authorities, and then they report the loopholes in the system. If the ethical hackers realize that there is something that is wrong in the network, they report the happening to the relevant authorities and the necessary action is taken. This is a job that requires people with relevant networking skills such as Social engineering, Linux and cryptography among others.
Ethical hackers are skilled people who are given access to the network, by relevant authorities, and then they report the loopholes in the system. If the ethical hackers realize that there is something that is wrong in the network, they report the happening to the relevant authorities and the necessary action is taken. This is a job that requires people with relevant networking skills such as Social engineering, Linux and cryptography among others.
73. The Top 5 Reasons to Back up Exchange Online
 Still don’t back up Exchange Online? Learn why you need a dedicated backup solution and not just native Microsoft native tools to ensure timely recoveries.
Still don’t back up Exchange Online? Learn why you need a dedicated backup solution and not just native Microsoft native tools to ensure timely recoveries.
74. Why Compliance and Data Protection is Important in the Blockchain Space
 Interview discussing why compliance and data protection is important in the blockchain space
Interview discussing why compliance and data protection is important in the blockchain space
75. Glossary of Security Terms: Public-key Cryptography
 Public-key cryptography — or asymmetric cryptography — is a cryptographic system in which keys come in pairs. The transformation performed by one of the keys can only be undone with the other key. One key (the private key) is kept secret while the other is made public.
Public-key cryptography — or asymmetric cryptography — is a cryptographic system in which keys come in pairs. The transformation performed by one of the keys can only be undone with the other key. One key (the private key) is kept secret while the other is made public.
76. How Fintech Companies Can Protect Data Privacy While Onboarding
 Taking advantage of these insights can empower fintechs to locate and approve new customers while mitigating friction and streamlining the customer journey.
Taking advantage of these insights can empower fintechs to locate and approve new customers while mitigating friction and streamlining the customer journey.
77. Glossary of Security Terms: HMAC
 HMAC is a protocol used for cryptographically authenticating messages. It can use any kind of cryptographic functions, and its strengh depends on the underlying function (SHA1 or MD5 for instance), and the chosen secret key. With such a combination, the HMAC verification algorithm is then known with a compound name such as HMAC-SHA1.
HMAC is a protocol used for cryptographically authenticating messages. It can use any kind of cryptographic functions, and its strengh depends on the underlying function (SHA1 or MD5 for instance), and the chosen secret key. With such a combination, the HMAC verification algorithm is then known with a compound name such as HMAC-SHA1.
78. Formjacking Attacks: Defention and How To Prevent It
 Formjacking attacks are designed to steal financial details from payment forms. Learn how it affects your business and tips to prevent a formjacking attack.
Formjacking attacks are designed to steal financial details from payment forms. Learn how it affects your business and tips to prevent a formjacking attack.
79. Cloud Security Strategies For Small Businesses
 If you work from home and use cloud solutions to archive business documents, who is responsible for Cloud Security
If you work from home and use cloud solutions to archive business documents, who is responsible for Cloud Security
80. European User Data is Shared 376 Times Per Day on Average
 Violation of private data and its commercial exchange are recurrent issues in the online world. In this thread, our community discusses personal data share.
Violation of private data and its commercial exchange are recurrent issues in the online world. In this thread, our community discusses personal data share.
81. Glossary of Security Terms: HPKP
 HTTP Public Key Pinning (HPKP) is a security feature that tells a web client to associate a specific cryptographic public key with a certain web server to decrease the risk of MITM attacks with forged certificates.
HTTP Public Key Pinning (HPKP) is a security feature that tells a web client to associate a specific cryptographic public key with a certain web server to decrease the risk of MITM attacks with forged certificates.
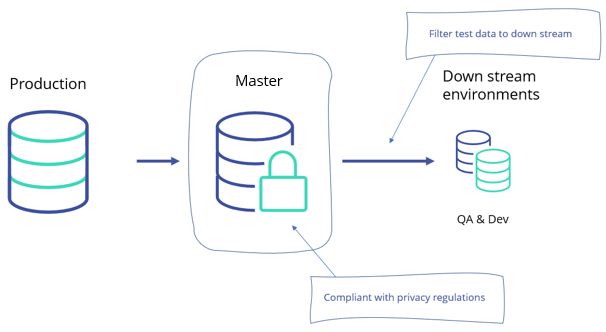
82. Data Masking: How it Can be Implemented Correctly
83. Using Unmasked Production Data For Testing Leaves Your At Risk For Data Breaches
84. The 5 Pillars of Cybersecurity for the Hidden Dangers We Confront Every Day
 Cyber protection is the integration of data protection and cybersecurity — a necessity for safe business operations in the current cyberthreat landscape.
Cyber protection is the integration of data protection and cybersecurity — a necessity for safe business operations in the current cyberthreat landscape.
85. How to Revolutionize Data Security Through Homomorphic Encryption
 For decades, we have benefited from modern cryptography to protect our sensitive data during transmission and storage. However, we have never been able to keep the data protected while it is being processed.
For decades, we have benefited from modern cryptography to protect our sensitive data during transmission and storage. However, we have never been able to keep the data protected while it is being processed.
86. Glossary of Security Terms: TOFU
 Trust On First Use (TOFU) is a security model in which a client needs to create a trust relationship with an unknown server. To do that, clients will look for identifiers (for example public keys) stored locally. If an identifier
is found, the client can establish the connection. If no identifier is found, the client can prompt the user to determine if the client should trust the identifier.
Trust On First Use (TOFU) is a security model in which a client needs to create a trust relationship with an unknown server. To do that, clients will look for identifiers (for example public keys) stored locally. If an identifier
is found, the client can establish the connection. If no identifier is found, the client can prompt the user to determine if the client should trust the identifier.
87. Glossary of Security Terms: Forbidden Response Header Name
 A forbidden response header name is an HTTP header name (either
A forbidden response header name is an HTTP header name (either Set-Cookie or Set-Cookie2) that cannot be modified programmatically.
88. Practices Used in eLearning Video-Content Protection
 Find out here how to provide eLearning content security which is needed with the majority of data in open access.
Find out here how to provide eLearning content security which is needed with the majority of data in open access.
89. Glossary of Security Terms: HTTPS
 HTTPS (HyperText Transfer Protocol Secure) is an encrypted version of the HTTP protocol. It uses SSL or TLS to encrypt all communication between a client and a server. This secure connection allows clients to safely exchange sensitive data with a server, such as when performing banking activities or online shopping.
HTTPS (HyperText Transfer Protocol Secure) is an encrypted version of the HTTP protocol. It uses SSL or TLS to encrypt all communication between a client and a server. This secure connection allows clients to safely exchange sensitive data with a server, such as when performing banking activities or online shopping.
90. Glossary of Security Terms: Hash
 The hash function takes a variable length message input and produces a fixed-length hash output. It is commonly in the form of a 128-bit "fingerprint" or "message digest". Hashes are very useful for cryptography — they insure the integrity of transmitted data. This provides the basis for HMAC's, which provide message authentication.
The hash function takes a variable length message input and produces a fixed-length hash output. It is commonly in the form of a 128-bit "fingerprint" or "message digest". Hashes are very useful for cryptography — they insure the integrity of transmitted data. This provides the basis for HMAC's, which provide message authentication.
91. 5 Data Breach Safety Measures That are Essential to Every Business
 Data breaches can tank even the most successful businesses. Here are the 5 most important things your business should do after a data breach.
Data breaches can tank even the most successful businesses. Here are the 5 most important things your business should do after a data breach.
92. Cybersecurity 101: How to Protect Your Data From Phishing Attacks
 Never click any links or attachments in suspicious emails. If you receive a suspicious message from an organization and worry the message could be legitimate.
Never click any links or attachments in suspicious emails. If you receive a suspicious message from an organization and worry the message could be legitimate.
93. A New Study On Data Privacy Reveals Information About Cybersecurity Efforts
 A study revealed by Cisco shows that most organizations around the world were unprepared for the increase in remote work.
A study revealed by Cisco shows that most organizations around the world were unprepared for the increase in remote work.
94. Glossary of Security Terms: Preflight Request
 A CORS preflight request is a CORS request that checks to see if the CORS protocol is understood and a server is aware using specific methods and headers.
A CORS preflight request is a CORS request that checks to see if the CORS protocol is understood and a server is aware using specific methods and headers.
95. E-commerce Cybersecurity - Enhancing Data Protection in 2021
 In 2020, the COVID-19 pandemic has completely changed the situation in the shopping industry: both e-commerce and brick-and-mortar were affected
In 2020, the COVID-19 pandemic has completely changed the situation in the shopping industry: both e-commerce and brick-and-mortar were affected
96. Glossary of Security Terms: Transport Layer Security
 Transport Layer Security (TLS), formerly known as Secure Sockets Layer (SSL), is a protocol used by applications to communicate securely across a network, preventing tampering with and eavesdropping on email, web browsing, messaging, and other protocols. Both SSL and TLS are client / server protocols that ensure communication privacy by using cryptographic protocols to provide security over a network. When a server and client communicate using TLS, it ensures that no third party can eavesdrop or tamper with any message.
Transport Layer Security (TLS), formerly known as Secure Sockets Layer (SSL), is a protocol used by applications to communicate securely across a network, preventing tampering with and eavesdropping on email, web browsing, messaging, and other protocols. Both SSL and TLS are client / server protocols that ensure communication privacy by using cryptographic protocols to provide security over a network. When a server and client communicate using TLS, it ensures that no third party can eavesdrop or tamper with any message.
97. Glossary of Security Terms: Robots.txt
 Robots.txt is a file which is usually placed in the root of any website. It decides whether crawlers are permitted or forbidden access to the web site.
Robots.txt is a file which is usually placed in the root of any website. It decides whether crawlers are permitted or forbidden access to the web site.
98. Glossary of Security Terms: CSP
 A CSP (Content Security Policy) is used to detect and mitigate certain types of website related attacks like XSS and data injections.
A CSP (Content Security Policy) is used to detect and mitigate certain types of website related attacks like XSS and data injections.
99. Glossary of Security Terms: SQL Injection
 SQL injection takes advantage of Web apps that fail to validate user input. Hackers can maliciously pass SQL commands through the Web app for execution by a backend database.
SQL injection takes advantage of Web apps that fail to validate user input. Hackers can maliciously pass SQL commands through the Web app for execution by a backend database.
100. The Trouble with FIPS
 FIPS 140 sets the standard for cryptography used in the United States, but it's got problems. Because of FIPS, we all have problems.
FIPS 140 sets the standard for cryptography used in the United States, but it's got problems. Because of FIPS, we all have problems.
101. Major Reasons Why You Have Wi-Fi Dead Zones
 In the event that you have certain rooms or regions in your home where the Wi-Fi signal is moderate or nearly non-existent, you may have a Wi-Fi no man’s land. Does it take everlastingly to stack a page on the PC in your room? Is it practically difficult to watch Netflix in the cellar? No man’s lands and moderate zones can cause your gushing sticks, PCs, and savvy home gadgets to run ineffectively, conflictingly, or in some cases, not under any condition.
In the event that you have certain rooms or regions in your home where the Wi-Fi signal is moderate or nearly non-existent, you may have a Wi-Fi no man’s land. Does it take everlastingly to stack a page on the PC in your room? Is it practically difficult to watch Netflix in the cellar? No man’s lands and moderate zones can cause your gushing sticks, PCs, and savvy home gadgets to run ineffectively, conflictingly, or in some cases, not under any condition.
102. On The Verge of Economic Change: An Interview with Dr Sebastian Bürgel
 It’s been over a year since COVID-19 appeared, and it’s still painfully apparent that this crisis is far from over. In fact, it may even trigger the largest economic change since World War Two. According to Arthur D. Little, a management consultancy firm, COVID-19 has been the impetus for an economic shift from a resources-driven to technology-focused economic model, one where the principles of “green” and tech go hand-in-hand. In essence, it will be data, not natural resources, which plays the fundamental role in keeping the global economy running. One possible implication of this is a full-scale transition to a digital economy. Data will be the fuel which powers our lives – and emerging technologies like the Internet of Things (IoT) and smart technologies will have to hit the ground running.
It’s been over a year since COVID-19 appeared, and it’s still painfully apparent that this crisis is far from over. In fact, it may even trigger the largest economic change since World War Two. According to Arthur D. Little, a management consultancy firm, COVID-19 has been the impetus for an economic shift from a resources-driven to technology-focused economic model, one where the principles of “green” and tech go hand-in-hand. In essence, it will be data, not natural resources, which plays the fundamental role in keeping the global economy running. One possible implication of this is a full-scale transition to a digital economy. Data will be the fuel which powers our lives – and emerging technologies like the Internet of Things (IoT) and smart technologies will have to hit the ground running.
103. How To Handle Every Ransomware Challenge With Ease Using These Tips
 There was nothing in particular that should have drawn attention to the two individuals sitting for drinks at the bar in Reno. Just two old colleagues catching up over some drinks.
There was nothing in particular that should have drawn attention to the two individuals sitting for drinks at the bar in Reno. Just two old colleagues catching up over some drinks.
104. Glossary of Security Terms: Key
 A key is a piece of information used by a cipher for encryption and/or decryption. Encrypted messages should remain secure even if everything about the cryptosystem, except for the key, is public knowledge.
A key is a piece of information used by a cipher for encryption and/or decryption. Encrypted messages should remain secure even if everything about the cryptosystem, except for the key, is public knowledge.
105. Glossary of Security Terms: Reporting Directive
 CSP reporting directives are used in a Content-Security-Policy header and control the reporting process of CSP violations.
CSP reporting directives are used in a Content-Security-Policy header and control the reporting process of CSP violations.
106. New Data Privacy Laws Are an Opportunity, Not a Threat

107. Glossary of Security Terms: Digital Сertificate
 A digital certificate is a data file that binds a publicly known cryptographic key to an organization. A digital certificate contains information about an organization, such as the common name (e.g., mozilla.org), the organization unit (e.g., Mozilla Corporation), and the location (e.g., Mountain View).
A digital certificate is a data file that binds a publicly known cryptographic key to an organization. A digital certificate contains information about an organization, such as the common name (e.g., mozilla.org), the organization unit (e.g., Mozilla Corporation), and the location (e.g., Mountain View).
108. Glossary of Security Terms: Datagram Transport Layer Security
 Datagram Transport Layer Security (DTLS) is a protocol used to secure datagram-based communications. It's based on the stream-focused Transport Layer Security (TLS), providing a similar level of security. As a datagram protocol, DTLS doesn't guarantee the order of message delivery, or even that messages will be delivered at all. However, DTLS gains the benefits of datagram protocols, too; in particular, the lower overhead and reduced latency.
Datagram Transport Layer Security (DTLS) is a protocol used to secure datagram-based communications. It's based on the stream-focused Transport Layer Security (TLS), providing a similar level of security. As a datagram protocol, DTLS doesn't guarantee the order of message delivery, or even that messages will be delivered at all. However, DTLS gains the benefits of datagram protocols, too; in particular, the lower overhead and reduced latency.
109. Glossary of Security Terms: Symmetric-Key Cryptography
 Symmetric-key cryptography is a term used for cryptographic algorithms that use the same key for encryption and for decryption. The key is usually called a "symmetric key" or a "secret key".
Symmetric-key cryptography is a term used for cryptographic algorithms that use the same key for encryption and for decryption. The key is usually called a "symmetric key" or a "secret key".
110. Glossary of Security Terms: Decryption
 In cryptography, decryption is the conversion of ciphertext into cleartext.
In cryptography, decryption is the conversion of ciphertext into cleartext.
111. Glossary of Security Terms: Forbidden Header Name
 A forbidden header name is the name of any HTTP header that cannot be modified programmatically; specifically, an HTTP request header name (in contrast with a Forbidden response header name).
A forbidden header name is the name of any HTTP header that cannot be modified programmatically; specifically, an HTTP request header name (in contrast with a Forbidden response header name).
112. Glossary of Security Terms: OWASP
 OWASP (Open Web Application Security Project) is a non-profit organization and worldwide network that works for security in Free Software, especially on the Web.
OWASP (Open Web Application Security Project) is a non-profit organization and worldwide network that works for security in Free Software, especially on the Web.
113. 10 Ways to Reduce Data Loss and Potential Downtime Of Your Database
 In this article, you can find ten actionable methods to protect your mission-critical database.
In this article, you can find ten actionable methods to protect your mission-critical database.
114. Handling Sensitive Data: A Primer
 Properly securing sensitive customer data is more important than ever.
Properly securing sensitive customer data is more important than ever.
115. Glossary of Security Terms: Certificate Authority
 A certificate authority (CA) is an organization that signs digital certificates and their associated public keys. This certifies that an organization that requested a digital certificate (e.g., Mozilla Corporation) is authorized to request a certificate for the subject named in the certificate (e.g., mozilla.org).
A certificate authority (CA) is an organization that signs digital certificates and their associated public keys. This certifies that an organization that requested a digital certificate (e.g., Mozilla Corporation) is authorized to request a certificate for the subject named in the certificate (e.g., mozilla.org).
116. Using Immutable Storage to Protect Data Against Ransomware
 The number of ransomware attacks reaches new heights, making businesses believe that there’s no effective weapon in this fight. But there is. Immutable storage
The number of ransomware attacks reaches new heights, making businesses believe that there’s no effective weapon in this fight. But there is. Immutable storage
117. Glossary of Security Terms: CSRF
 CSRF (Cross-Site Request Forgery) is an attack that impersonates a trusted user and sends a website unwanted commands. This can be done, for example, by including malicious parameters in a URL behind a link that purports to go somewhere else:
CSRF (Cross-Site Request Forgery) is an attack that impersonates a trusted user and sends a website unwanted commands. This can be done, for example, by including malicious parameters in a URL behind a link that purports to go somewhere else:
118. What are the Key Stages of Data Protection Impact Assessment?
 A Data Protection Impact Assessment which is also referred to as Privacy Impact Assessments is a mandatory requirement for organizations to comply with.
A Data Protection Impact Assessment which is also referred to as Privacy Impact Assessments is a mandatory requirement for organizations to comply with.
119. A Complete Guide on How to Assess Risk and Run Contingency for your IT Infrastructure Needs
 IT risk assessment is one of the most crucial processes in your organization. Assessing risk and putting contingency plans in place helps run the organization smoothly.
IT risk assessment is one of the most crucial processes in your organization. Assessing risk and putting contingency plans in place helps run the organization smoothly.
120. 23 Cybersecurity Tips to Level up Your Data Privacy Game
 It's important to keep yourself up-to-date on the latest security measures. Cybercrime has increased, secure your data.
It's important to keep yourself up-to-date on the latest security measures. Cybercrime has increased, secure your data.
121. Data and DNA: Who Owns You?
 Data and DNA: With corporations able to accumulate information normally considered private on both of these fields, who should own that data and thus you?
Data and DNA: With corporations able to accumulate information normally considered private on both of these fields, who should own that data and thus you?
Thank you for checking out the 121 most read stories about Data Protection on HackerNoon.
Visit the /Learn Repo to find the most read stories about any technology.

